Receive your JavaScript security report
More no-brainers
CDN server security check
If the Javascript library is hosted on an external server (such as a Content Delivery Network or CDN), the security of your website depends on the security of the external server. That CDN better be secure!
Each external content server is given a security score that is based on a dozen non-intrusive checks in the following categories:
- (P) Patch management - a (visible) lag in software versions
- (B) Blacklisted - presence on a blacklist of servers that distribute malware (not spam)
- (S) SSL/TLS-configuration - weak encryption, expired certificate, etc.
- (H) SSH-configuration - weak cryptokey
- (W) Webserver configuration - unsafe HTTP-methods
- (N) Nameserver configuration - zone transfer
- (D) Design issues - logon over plain-text connections, etc.
At the beginning of the vulnerability assessment, every server is given a security score of 100 points. For each security issue encountered, points are subtracted. If a vulnerability can’t be assessed, no points are lost. Thus, the security score is based on falsification: it is assumed that the server is secure, unless proof of the opposite is found.
An example of the server scores are shown in figure 1. Each unique combination of an IP-address and a dns-name is called a ‘server’. The security scores are colored according to the traffic-light model. Green is OK (0 or 1 no-brainers found), red is high risk (5 or more no-brainers found). If a server cannot be connected to, no security score is given (blank).
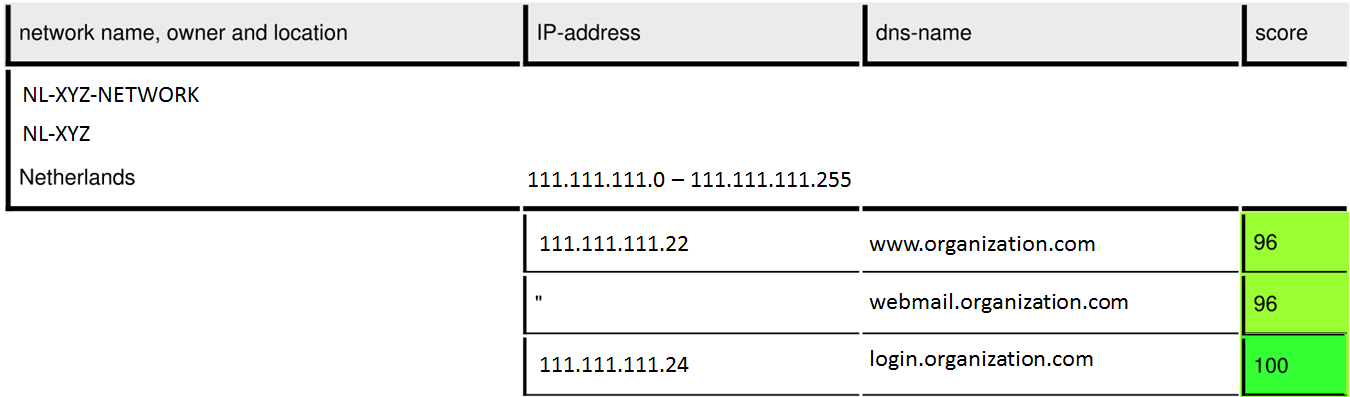
Figure 1. Example list of servers and their security score, derived from the basic security check.
The underlying idea is that with a few checks a quick indication is obtained of possibly vulnerable servers. The security score itself is no hard evidence but is a risk indicator that should give rise to further investigation.